Securitatea
datelor
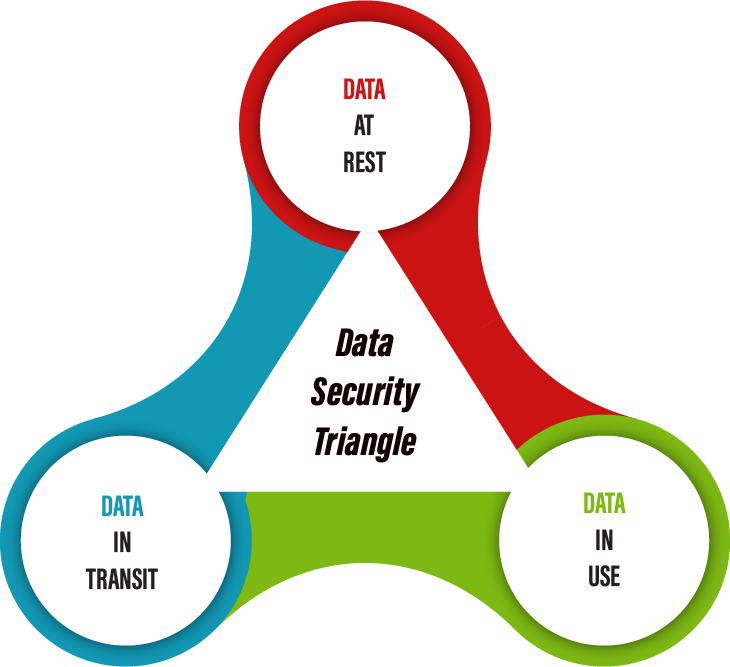
Descoperă soluţiile certSIGN pentru securitatea datelor, indiferent unde se găsesc acestea – stocate, utilizate sau în tranzit!
Securitatea centrată pe date se concentrează pe ceea ce trebuie protejat și pe aplicarea formei adecvate de protecție, indiferent unde se găsesc datele, dacă sunt stocate, utilizate sau în tranzit.
Caracteristica definitorie a securităţii centrate pe date este aceea că protecția se aplică datelor în sine, prin mecanisme de clasificare, de control al accesului, de criptare sigură și, atunci când este necesar, de ștergere sigură.

Trust4Mobile este o soluţie destinată dispozitivelor mobile ce asigură securizarea comunicaţiilor voce mesaje şi conferinţă prin intermediul criptării, fiind acreditată pentru protecţia informaţiilor clasificate la nivel naţional cu nivel de secretizare „SECRET DE SERVICIU” şi inclusă în „Catalogul naţional de produse şi profile de protecţie INFOSEC” publicat de Agenția Națională de Securitate (ORNISS).
Destinată comunicaţiilor securizate între dispozitivele mobile, Trust4Mobile se adresează mediul de afaceri din perspectiva punerii la dispoziţie a unui mediu colaborativ angajaţilor, în vederea creşterii eficienţei, cât şi în raport cu partenerii de afaceri. Aplicaţia Trust4Mobile dispune de o interfaţă intuitivă şi permite cu uşurinţă utilizatorilor să iniţieze apeluri, să transmită mesaje şi fişiere criptate, precum şi să iniţieze sau să participe în conferinţe ad-hoc. Trust4Mobile dispune şi de o interfaţă de administrare prin intermediul căreia se pot gestiona utilizatorii, se pot crea grupuri sau organizaţii.
Disponibilă în Google Play şi App Store şi compatibilă cu majoritatea dispozitivelor (versiuni de sisteme de operare), aplicaţia Trust4Mobile utilizează serviciul de date mobile 3G/4G/5G sau WiFi.



shellSAFE este o suită completă de aplicaţii pentru crearea de semnătură electronică şi protejarea informațiilor pe stațiile desktop. Cu ajutorul shellSAFE poţi crea una sau mai multe semnături electronice (cosemnătură / contrasemnătură), cripta / decripta documente pentru unul sau mai mulţi destinatari, securiza automat corespondenţa prin integrare în clientul de e-mail, şterge fişiere într-o manieră securizată, verifica online strarea certificatelor digitale şi apela la servicii de marcare temporală.
shellSAFE permite conectarea şi transmiterea facilă a mesajelor către emailerSAFE, serviciu de e-mail cu notificare autorizată. Componentele individuale ale shellSAFE îţi asigură securitatea optimă pentru toate activităţile de prelucrare a informaţiei pe care le desfăşori.
shellSAFE este acreditată pentru protecţia informaţiilor clasificate la nivel NATO şi naţional, fiind inclusă în Catalogul NATO (NIAPC – NATO Information Assurance Product Catalogue) şi în Catalogul naţional cu pachete, produse şi profile de protecţie INFOSEC, publicat de Agenția Națională de Securitate (ORNISS).

shellSAFE Verify este un utilitar gratuit cu care se poate verifica semnătura electronică şi care permite vizualizarea documentelor semnate electronic. Este folosit în cazul în care nu doreşti o semnare electronică a informaţiilor însă primeşti asemenea date semnate electronic. Aplicaţia poate verifica orice tip de semnătură electronică, indiferent de soluţia folosită pentru crearea acesteia.
Nu poţi accesa documente semnate electronic folosind shellSAFE Verify dacă:

emailerSAFE SE este un produs software pentru securizarea poştei electronice, cu confirmare, având valoare legală. Sistemul emailerSAFE garantează faptul că un e-mail a fost transmis de către expeditor şi a fost primit de către destinatar fără ca acest lucru să mai poată fi negat ulterior.
Mesajele pe care le schimbi cu partenerii tăi conţin adesea informaţii de importanţă critică pentru buna desfăşurare a afacerilor tale. emailerSAFE oferă mecanisme pentru:



Mobilitatea în România devine din ce în ce mai mult un trend de transformare digitală a companiilor și a mediului de afaceri. Acest fenomen se realizează prin schimbarea modului în care angajații lucrează și a felului în care aceștia interacționează în vederea îndeplinirii activităților de zi cu zi. Mobilitatea devine sub această formă una dintre principalele priorități de creștere a eficienţei și a performanţei la nivelul firmelor și totodată impune definirea de noi standarde de securitate în ceea privește protecția informațiilor. Compania certSIGN a dezvoltat în ultimii 6 ani o serie de parteneriate cu producători de top de soluții de tip Unified Endpoint Management, soluții ce permit administrarea centralizată a întregii flote de dispozitive cu sisteme de operare diferite, Android, iOS, Windows și MacOS.
Soluțiile de tip UEM din protofoliul certSIGN permit implementarea de standarde de securitate ce vizează protejarea datelor pornind de la:
Experiența echipei certSIGN poate asigura implementarea celor mai variate cerințe de business și de securitare, acoperind tot ciclul de viață al unui dispozitiv mobil din momentul scoaterii din cutie, configurării pe bază de IMEI și înrolării automate în platforme de administrare UEM, instalării și configurării de aplicații de business, precum și izolarea acestora față de mediul personal în vederea implementării de programe BYOD. Expertiza certSIGN asigură furnizarea de servicii de suport de nivel 1, 2 și 3 pentru toate soluțiile comercializate, completând astfel portofoliul de servicii profesionale puse la dispoziția companiilor din România.


Protejarea datelor pe toată durata de viață a fost întotdeauna o preocupare majoră a noastră. Prin programul certFHE, ne propunem să cercetam și să inovăm algoritmi specifici criptografiei homomorfice, meniți să permită prelucrarea datelor în format criptat, fară a fi necesară decriptarea lor în prealabil.
certSIGN a obținut un patent de invenție pentru o metodă de criptare homomorfică a datelor care permite procesarea acestora fără a le decripta. Patentul a fost acordat de Biroul de Patente și Mărci al Statelor Unite ale Americii și are numărul US10454668 din 22.10.2019.

Bd. Tudor Vladimirescu nr. 29 A, AFI Tech Park 1, Sector 5, Bucureşti, România, 050881
Șos. Olteniței, nr. 107A,
Sector 4, București, România, 041303
Utile
Politici și proceduri
Asistenţă
Sediu central:
Bd. Tudor Vladimirescu nr. 29 A, AFI Tech Park 1
Sector 5, Bucureşti, România, 050881
Sediu social:
Șos. Olteniței, nr. 107A
Sector 4, București, România, 041303
Nr. Reg. Comerțului:
J40/484/2006
Cod de înregistrare fiscală:
RO18288250

TOKEN-urile pentru semnătura electronică pot fi utilizate în continuare de ORICE deținător de certificat digital, în aceleași condiții ca pana in prezent. Nu este necesara schimbarea tokenului pentru semnătură.
Mesajul prezent pe site-ul ANAF privind tokenurile JWT și OPAQUE se adresează EXCLUSIV persoanelor din domeniul tehnic IT: dezvoltatorilor de aplicații ce utilizează servicii web ce folosesc protocolul OAUTH. Daca nu faceți parte din aceasta categorie va rugăm ignorați mesajul.
Pentru verificarea informației vedeți si manualul de utilizare din mesajul de pe site-ul ANAF, pagina 2.
Nu ai găsit ce căutai? Descrie cât mai detaliat situația pentru care ai nevoie de un răspuns.
Detalii legate de semnătura electronică sunt disponibile pe pagina cu Răspunsurile pentru cele mai frecvente întrebări ale clienților.
Rapid pot fi aflate informații utile despre costuri, modalități de obținere, achiziție online, identificare video, instalare şi utilizare:
Sunt descrise și:
Nu ai găsit ce căutai? Descrie cât mai detaliat situația pentru care ai nevoie de un răspuns.
Detalii legate de modalitatea de personalizare semnăturii astfel încât în aspectul acesteia să fie incluse și informațiile solicitate de OUG 140/2020 cu privire la specialiștii din domeniile construcții, arhitectură și urbanism sunt disponibile pe pagina Creare aspect semnătură OUG 140/2020
De asemenea, alte informații legate de semnătura electronică sunt disponibile pe pagina cu
Răspunsurile pentru cele mai frecvente întrebări ale clienților
Nu ai găsit ce căutai? Descrie cât mai detaliat situația pentru care ai nevoie de un răspuns.
Pentru a obține de la certSIGN certificatul calificat de semnătură electronică, pentru semnarea documentelor din domeniile construcţii, arhitectură şi urbanism în conformitate cu OUG 140, sunt necesare:
DOCUMENTELE
Transmite-ne un mesaj și solicită documentele necesare pentru achiziția Kit-ului de semnătură. Vei primi din partea certSIGN un set de documente pe care trebuie să le completezi cu datele viitorului titular de certificat pentru semnătură.
Documentele originale semnate (2 exemplare) alături de copiile documentelor ce atestă încadrarea profesională trebuie prezentate către certSIGN. Pe scurt, sunt necesare:
ORIGINAL (2 exemplare, semnate): “Contract”, “Termeni și condiții generale”.
Pentru cazul documentelor transmise prin curier: “Declarația” completată după modelul certSIGN
COPIE pentru: Cartea de identitate a titularului, Certificatul de Înregistrare Fiscală, Documentul atestare profesională,
IDENTIFICAREA
În vederea identificării, persoana pe numele căreia certSIGN va emite certificatul digital calificat se va prezenta personal, cu actul de identitate original, la unul din reprezentanții certSIGN la nivel național sau la sediile certSIGN.
Alternativ, identificarea titularului de certificat se mai poate efectua și transmițând documentele de mai sus la sediul certSIGN însoțite obligatoriu de “Declarația” completată după modelul certSIGN (autentificată la notar sau atestată de un avocat în temeiul art.3 al.3 din legea 51/1995)
ATENTIE! Pentru fiecare Entitate emitentă ( ex. OAR, ISCIR etc) se emite câte un certificat pentru semnătură electronică!
Citește despre Semnătura electronică în construcţii, arhitectură şi urbanism
Nu ai găsit ce căutai? Descrie cât mai detaliat situația pentru care ai nevoie de un răspuns.
Detalii despre descărcarea certificatului titularului și a certificatului intermediar solicitate la înregistrarea pentru depunerea declarațiilor vamale folosind semnătura electronică sunt disponibile pe pagina Utilizarea certificatului de semnătură electronică în platforma Sistemul Informatic Integrat Vamal
Pentru acces în Sistemul Informatic Integrat Vamal (SIIV) la secțiunile AES și NCTS5 RO UMG Trader Producție trebuie să încărci în platforma UMG Trader, într-unul dintre formatele .cer/.der/.crt, certificatul tău calificat și certificatul intermediar al autorității care a emis certificatul.
CUM OBȚIN CERTIFICATUL PERSONAL ÎN FORMATUL SOLICITAT?
Conectează token-ul sau deschide aplicația Paperless vToken și urmează acești pași.
Nu ai tokenul/ aplicația la dispoziție?
Accesează link-ul https://registru.certsign.ro/cgi-bin/pubra/pubra/get_cert , completează datele din certificatul calificat (nume și prenume complet sau adresa de email), identifică certificatul cu care dorești înregistrarea și apasă butonul „Descarcă DER”.
Certificatul calificat se va descărca în mod automat în format .crt.
CUM OBȚIN CERTIFICATUL INTERMEDIAR ÎN FORMATUL SOLICITAT?
Pentru descărcarea certificatului autorității intermediare certSIGN accesează unul dintre link-urile:
Certificatul intermediar se va descărca în mod automat în format .crt.
Nu ai găsit ce căutai? Descrie cât mai detaliat situația pentru care ai nevoie de un răspuns.
IDENTIFICAREA VIDEO NEASISTATĂ este un element important în procesul de obținere a semnăturii electronice cu certificat digital calificat.
Procedura de identificare este simplă, dar strictă. Ea poate fi făcută după efectuarea plății certificatului și doar urmând indicațiile furnizate de certSIGN, astfel:
AI FINALIZAT IDENTIFICAREA VIDEO, DAR N-AI PRIMIT NICIUN EMAIL?
În maxim 24 ore, după parcurgerea procesului de identificare video, vei fi informat pe e-mail cu privire la validarea/respingerea acestuia.
IDENTIFICAREA VIDEO A FOST RESPINSĂ?
Din partea certSIGN vei primi un email cu un nou link pentru reluarea procedurii de identificare video. Condițiile ce trebuie respectate sunt aceleași.
Nu ai găsit ce căutai? Descrie cât mai detaliat situația pentru care ai nevoie de un răspuns.
Codurile PIN/PUK reprezintă elemente de siguranță cu ajutorul cărora se folosește TOKEN-ul. Aceste coduri sunt confidențiale și nu trebuie dezvăluite nimănui, în nicio situație.
Codul PIN = Token Password este parola cu care se utilizează tokenul.
Codul PUK = Administrator Password este parola cu care se poate debloca tokenul.
NU AI PRIMIT CODUL PIN/PUK?
Transmiterea codurilor PIN/PUK pentru certificatul calificat PE TOKEN se poate face în 2 moduri:
ELECTRONIC – dacă adresa de e-mail asociată certificatului digital calificat pentru semnătura electronică a fost validată și este una personală (are elemente în componența sa ce pot face legătura cu titularul certificatului – ex: ion.popescu@).
Are 2 componente:
FZIC – în plic, prin curier – dacă adresa de e-mail asociată certificatului digital calificat pentru semnătura electronică NU a fost validată la completarea cererii de certificat sau dacă NU este una personală (nu are elemente în componența sa ce pot face legătura cu titularul certificatului – ex: office@).
AI UITAT CODUL PIN?
Pentru recuperarea codului PIN este nevoie de codul PUK al tokenului.
AI MACOS SI VREI SA SCHIMBI CODUL PIN AL TOKENULUI?
Urmează instrucțiunile de Schimbare a codului PIN pe MacOS
ATENŢIE! Sistemele de operare macOS Sonoma, Ventura și Monterey acceptă doar parole de maxim 8 caractere. Prin urmare, dacă folosești unul sin aceste sisteme de operare, la schimbarea codului PIN al TOKEN-ului, trebuie să pui o parolă de maxim 8 caractere.
Nu ai găsit ce căutai? Descrie cât mai detaliat situația pentru care ai nevoie de un răspuns.
Detalii legate de semnătura electronică sunt disponibile pe pagina cu Răspunsurile pentru cele mai frecvente întrebări ale clienților.
Rapid pot fi aflate informații utile despre costuri, modalități de obținere, achiziție online, identificare video, instalare şi utilizare:
Sunt descrise și:
Nu ai găsit ce căutai? Descrie cât mai detaliat situația pentru care ai nevoie de un răspuns.
Pentru obținerea documentului de confirmare trebuie sa parcurgi următoarele etape, în această ordine:
Urmărește unul dintre aceste tutoriale, în funcție de tipul de semnătură pe care îl ai.
Nu ai găsit ce căutai? Descrie cât mai detaliat situația pentru care ai nevoie de un răspuns.
Dacă ai nevoie și de alte informații pentru a alege ce tip de certificat calificat pentru semnătură electronică ți se potrivește verifică și informațiile din secțiunea: Ce semnătură aleg
Detalii legate de semnătura electronică sunt disponibile pe pagina cu Răspunsurile pentru cele mai frecvente întrebări ale clienților.
Rapid pot fi aflate informații utile despre costuri, modalități de obținere, achiziție online, identificare video, instalare şi utilizare:
Sunt descrise și:
Nu ai găsit ce căutai? Descrie cât mai detaliat situația pentru care ai nevoie de un răspuns.
Cum obții semnătura electronică în CLOUD?
Semnătura electronică se realizează cu ajutorul unui certificat digital calificat iar pentru obținerea certificatului în CLOUD trebuie parcurse etapele:
În cazul în care informațiile primite sunt corecte și complete, la adresa de email indicată în formularul de înregistrare, certSIGN va trimite două invitații:
Cu ajutorul acestor componente vei putea configura și utiliza semnătura electronică calificată în CLOUD. Dreptul de utilizare al semnăturii electronice în cloud va fi acordat după configurarea mecanismului de autorizare și crearea contului de utilizator în platforma de semnare Paperless webSIGN.
După realizarea pașilor din cele două invitații, la prima logare în contul tău din platforma de cloud, se emite certificatul digital.
* ATENŢIE! Dacă dorești să folosești certificatul în cloud la instituții precum ANAF, SPV, AFM etc. pentru semnarea documentelor / autentificarea la platforme web ce solicită acest lucru, o poți face local, nu în cloud, pe sistem de operare Windows. În afară de certificatul în cloud și Windows (versiuni 8.1, 10 sau 11) ai nevoie de aplicația tokenului virtual Paperless vToken (inclusă în pachet).
Cum obții semnătura electronică cu TOKEN?Semnătura electronică se realizează cu ajutorul unui certificat digital calificat, iar pentru obținerea certificatului pe TOKEN trebuie parcurse etapele:
|